Loading
Senthorus MDR for Microsoft Sentinel boosts your cybersecurity, ensuring swift deployment and maximizes your investment in Microsoft licenses from day one.
Senthorus provides over 900+ Custom Alerts and 300+ custom data connectors above and beyond what is currently available out of the box. This allows for finely tuned high-fidelity alerting increasing time to detection and reducing time to reediate, complete visibility, with auditable operations ensuring you retain full data control.
With our real-time alerts and adept management of cyber incidents, we bolster your business's resilience while maintaining transparency and reducing to a minimum noisy distractions by prioritizing notifications that matter.
Our service assures best practice policy application, advanced threat hunting, all under your control via our intuitive portal.
At Senthorus, we get it right - the first time.
Key Services Delivered:
- Express onboarding with log optimization to minimize spend
- Swiss-based 24x7 SOC Monitoring & Investigation in Microsoft Sentinel
- Proactive Alert Tuning
- Real-time Threat Intelligence Enrichment
- ITSM Ticketing integration
- Integrated Real-Time Customer Portal
- Regular reporting with easy-to-understand dashboards
- Application of best practice policy and alert recommendations
- Close investigated alerts with classifications to see trends
- “Concierge” services are included for any custom requests
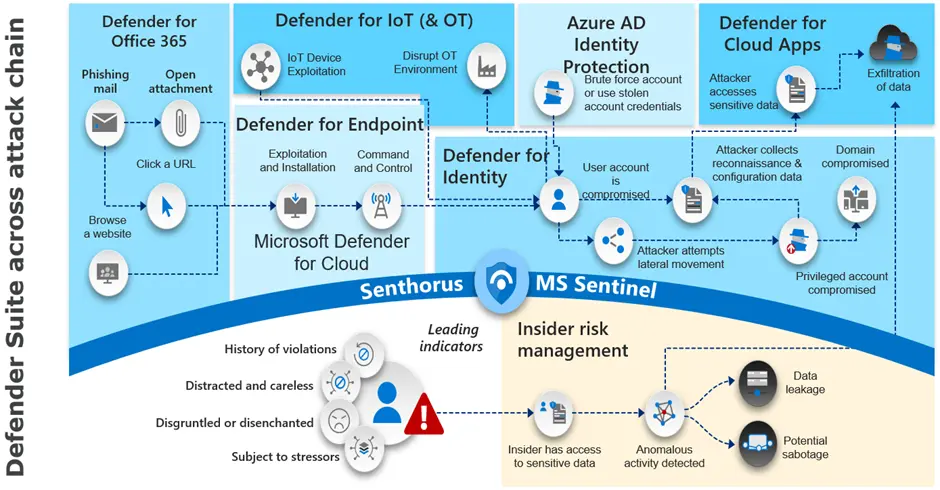
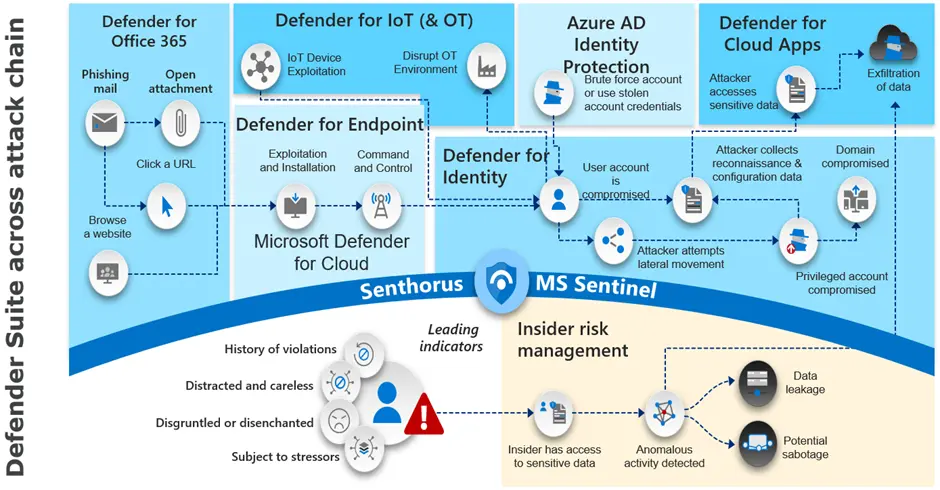
Beyond Microsoft Sentinel SIEM
Beyond Microsoft Sentinel SIEM, a complete portfolio of Microsoft security-focused SOC services, including a customized deployment of Microsoft security tools that can be incorporated according to your landscape:
Contact our expert
Olivier SPIELMANN
General Manager Senthorus
Meet Oliver SPIELMANN, our General Manager for Senthorus. Contact Oliver to discuss how he can help propel your cybersecurity initiatives forward.
